Taking the venerable quote from Harry Truman,” If you cannot convince them, confuse them”, Facebook will change its coverage so that three-fourths of its total user base (including those in the United States and Canada) will not be able to file a complaint in Ireland, where Facebook’s international headquarters lies. So European Union residents are covered by the GDPR rules. This change will continue to keep Facebook in the news as being untrustworthy, and could cause the U.S. congress to add more stringent laws.
Tag Archives: unethical behavior
Crowdsourcing Companies Likely Can’t Boost YouTube Views. Can Proxy Servers?
The old adage “If it seems to be too good to be true, it probably is”. That is, it’s NOT true. Crowdsourcing companies promise a lot more than they can deliver. Our previous post proved to be way too optimistic when we tried to get a couple of those companies to actually deliver those views. What we found was that some proxy servers MIGHT do so.
However, it seems that proxy servers are as much of a bag of snakes as crowdsourcing entities. We noted during our experiments with crowdsourcing companies that some of them proposed to use proxy servers, or actually did so, but they apparently did not succeed in adding more than a handful of views. That apparently was because YouTube is too clever, and they disqualified most of the views for a variety of reasons. For example, if the crowdsource operative used a proxy server located in a country other than his/her own (which they could tell if the visiting IP was from one country in one time zone but the time of the computer to which the IP was attached was set to a different time zone), YouTube disqualified those views.
The other challenge is that most proxy server folks want to be paid in Bitcoin. While you can use dollars or credit cards or gift cards at sites like Paxful, they can be pretty expensive.
The bottom line is that many owners of YouTube channels may find it too expensive and time-consuming to boost their view counts via crowdsourcing or proxy servers.
Those Who Live by Google Analytics Shall Die by Google Analytics
We at Wild Bill Web Enterpises have been tracking the visitors (and other metrics) for our three websites–including TechnologyBloopers, WhyMenDieYoung, and Wilddancer—on a weekly basis using Google Analytics and on a monthly basis using our ISP for nearly two years, and are baffled by the helter-skelter, all-over-the-map, random-looking numbers Google Analytics is providing us. Apparently this is a common problem, with a lot of possible causes, including some possibilities that could be our fault (well, the lack of useful guidance from Google and other sources isn’t really OUR fault). And it isn’t that our visitor volume is so high that we are the victim of Google’s sampling process. But we, and probably millions of other website developers, find it highly difficult, even impossible, to make any decisions based on this data. Why don’t the Internet and the Web take advantage of the huge computing power of the hardware and software to provide reasonably accurate statistics so that we can make things easier and more productive for both us and our visitors?
Live by the Sword, Die by the Sword
But it’s already too late to put the sword back in its place. The Internet, the Worldwide Web, Google Search, social networks, and other on-line miracles have given billions of people capabilities they never had dreamed of. But in their haste the makers of these tools have also enabled evil-doers capabilities beyond the masses’ worst nightmares. History is full of other technological advances that have been used for both good and evil purposes, but more recently cyberattacks have permitted individuals or small groups, sitting in safety at their personal computing devices, to wreak havoc on millions of innocent victims. These cyberattacks appear to be increasing in frequency and scope of havoc. Most recently several news sources reported the charging of an Iranian hacker on March 24 of his 2013 attack on a dam in Rye Brook, NY, which he found vulnerable using a technique called Google Dorking. (The wheels of justice certainly turn slowly … especially compared with the speed of computers and their hacker masters!)
Apparently he did not use his knowledge to operate the sluice gate of this small dam (perhaps because it was disconnected from computer control at the time). And although this dam is in a rather backwater community (pun intended) and not much of a threat to national security or even significant injury to people or damage to property, the ability of the hacker to infiltrate the computer system demonstrates a capability to attack a much bigger and more dangerous dam or other strategic infrastructure such as an electric power grid.
The really scary thing is that almost certainly many other sectors are under similar attacks. One such sector is hospitals. Within the last two months the computer systems at the Hollywood Presbyterian Medical Center, the Methodist Hospital in Henderson, KY, and the MedStar Georgetown University Hospital in Washington, DC were crippled by cyberattacks. These were not minor incidents; the overall MedStar 10-hospital group has 30,000 staff and 6,000 affiliated doctors. And patients in critical condition could die from the delays caused by inoperative computer systems.
Another sector is financial. On March 29 hackers breached the security at two large law firms whose giant Wall Street banks and corporate clients are constantly dealing with confidential matters, knowledge of which could net hackers millions of dollars through insider trading.
The general populace can only hope that the responsible governmental agencies are working hard to identify strategic facilities throughout the U.S. and its allies, and alert vulnerable ones so they can take steps to minimize the dangers from Google Dorking and other hacker nastiness. And also hope that “white hat hackers” (the good guys)–the modern-day equivalent of yesteryears’ vigilantes—step up their activities. It would help considerably if these strategic facilities would reward these hackers for their efforts.
Bloopers Beyond Technology: Theft of Bangladesh Funds is a Comedy of Errors and Law-Breaking By Humans

Technology does not exist in a vacuum. It is created by humans of varying degrees of ability and honesty. And technology involving the Internet is generally so complex, and created under time pressure, that it is more error-prone than more cautious and patient people would like.
According to the New York Times, slack security at the New York Fed (that’s the Federal Reserve Bank of New York), which most folks would consider a bastion of safe-keeping, allowed a bunch of money ($81 million or $100 million or some such sum) that rightfully belonged to poverty-stricken Bangladesh to be misappropriated by Chinese hackers and transferred to the Philippines, where in turn it was apparently transferred by above-the-law banks to putatively money-laundering casinos, who made it vanish beyond any chance of recovery. We’re not making this up. Mere prose and still images can’t do it justice. And no fiction writer could have imagined a more twisted tale.
The comedy continues if one reads the Zero Hedge blog, which apparently specializes in spreading misinformation of all sorts, including calling a spade a spade when it might not be. Entertaining to most of the world, but not to a few officials during whose watch this debacle occurred or to starving citizens of Bangladesh.
“Fair Use” of Copyrighted Material Gets (a Little) Justice
Did Stephanie Lenz make a bag of money from her video that Universal would otherwise have made? It seems that actually Universal and Prince got a lot of free advertising out of it starting in 2007, no? A U.S. Circuit Court of Appeal has just struck a blow against the hubris of music publishers such as Universal who send out takedown notices at the drop of a hat. If every YouTube (or Vimeo et al) video that borrowed a little, or even a lot, triggered so much legal argy-bargy, there wouldn’t be enough lawyers and judges on the planet to deal with it all. Similarly for the print world, and look at all the examples of “the pot calling the kettle black”:
-Google violated copyrights wholesale by scanning millions of books; but didn’t that provide a service to humanity by making intellectual content available for out-of-print volumes?
-Facebook was essentially a college Freshman Register; could it have been sued by thousands of universities collectively?
-Amazon’s Kindle refuses to let owners copy even one word. So all students writing term papers are back to the archaic 3×5 cards in the digital age. How stupid can they be, especially in the days of the Turnitin plagiarism checker technology?
Will There be a Useful Truce Among Ads and Ad Blockers and Ad Blocker-Blockers?
History buffs may liken this situation to the spy-and-counter-spy among countries. It surely seems to us at Technology Bloopers to be a great waste of resources and a great inconvenience to the more than 3 billion current users of the Internet today. Most users have already been spoiled by the “free” goodies they enjoy in return for their viewing increasing volumes of advertising. This arrangement has been around for at least 150 years in newspaper and magazine publishing, although most of the important hard-copy publications make their revenue from a combination of subscription fees and advertising purchases. By contrast, the much more recent Internet is mostly free to users and paid for by advertisers. Some interesting exceptions are Wikipedia, language-learning site Yabla, and purchase or rental of plugins and themes for WordPress. In the opinion of Technology Bloopers, there are many Internet sites for which users would pay reasonable fees, which would reduce the conflict among the titans of Silicon Valley. Google has contributed great gobs of technology but financed it heavily with ads. But users have had their fill of ads, leading to a rapid growth of ad blocking software. And some of the ads are so intrusive (the ones on SpanishDict.com are the worst in our experience, interrupting users with highly-distracting audio and video) that they cry out for ad blockers … and boycotting of such sites in favor of more ones that are less obnoxious. The advertisers have been spooked by this software, leading to a rapid growth of software that undoes the blocking. Most recently Apple has jumped into the fray with its own ad blockers, which is a welcome counter-force, though actually Apple has its own ads buried in its Apps, so the only beneficiary is Apple, while Google loses business and consumers continue to be annoyed by ads.
Anything is Funny if it Didn’t Happen to You
But though most people can recover from having their credit card data compromised (or perhaps weren’t personally affected by it), they might not recover so well from having their marriage destroyed, so perhaps the most poignant of recent hacks was the one of the Ashley Madison extramarital affair website. Most recently Ashley Madison users filed class action lawsuits in Canada and the US, which will almost certainly destroy the company and at a minimum disgrace its parent company Avid Life Media Ironically, the hackers had originally not tried to destroy the whole thing but to force more ethical behavior on it, and when the company stonewalled the hackers carried out their threat of disclosure. Another example of hubris … which has at a minimum forced the CEO of Avid Life Media to resign.
We Have Met the Enemy and He Is Us – Redux
If something can go wrong, it will. And in the millions, nay billions, nay trillions (or more) of lines of code that comprise the Internet and its many websites (the total reached 1 billion in September 2014) that there are countless opportunities for errors or loopholes that let the bad guys (AKA hackers) wreak havoc. And that havoc can affect millions of innocent victims. The extent of the hacking during the past few years is enormous as can be seen from an interesting infograph.
In another recent episode that demonstrated the increasing ease of hacking, shady securities traders stole announcements from Business Wire, PR Newswire, and Marketwired after it was uploaded by the companies but before it was released to the public, and made millions by trading ahead of the public. (The former, harder method was to recruit company “insiders” to get advance tips.)
And there may be some recent disasters that were self-inflicted, e.g., the outages at the NYSE and United Airlines. Absent an identified villain, we would attribute those to faulty code that is so complex it is impossible to test thoroughly and to change as the environment changes.
Hacking has even become so widespread, and apparently so easy, that one of the leading anti-hacking software companies, the Italian company Hacking Team was recently hacked itself.
Even more scary is the almost certain hacking by unfriendly nations’ government-sponsored hackers (China, Russsia, etc.). Some of it is stealing commercial intellectual property, which can undermine the US’s economic strength (and directly or indirectly its military strength). Other of it can be military secrets, the loss of which can compromise the national security.
In the ultimate irony, The Wall Street Journal pointed out that while the giant tech firms like Apple, Facebook, and Google encrypt their data they don’t cooperate with the US government to searches that are legal under the Fourth Amendment of the Constitution.
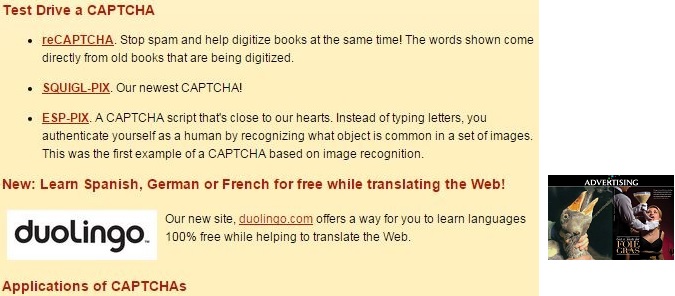
The Most Insidious Advertisement We’ve Seen (So Far)
Few would dispute the great usefulness of Google search. And most of us are willing to put up with the numerous ads that come along with the content. They are usually a small price to pay for the convenience and completeness of the information we seek. And we rarely have a choice of ads + free content vs. paid content. Sometimes the ads are distracting and/or invasive (especially ones with audio, video, or animation). But perhaps the worst ads are the ones that don’t look like ads at all. For example, the one in the graphic above, which is formatted to look just like the usable content itself. This strains the limits of ethics; at least in paper periodicals the advertisements are either clearly advertisements (as is easily seen by their formats) or are clearly labeled “ADVERTISEMENT”. Unless you truly need the content you found, we urge you to peruse other, more ethical, websites for your information needs. (It was interesting that we found this on a website dealing with CAPTCHA’s, which is another phenomenon of dubious merits.)