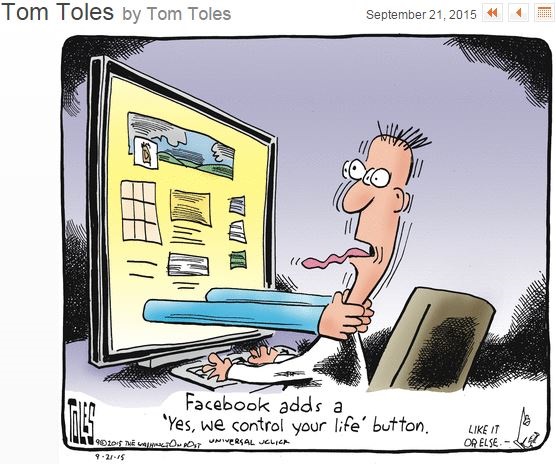
(sharing humor and a warning about ordering Google Pizza – from Joke Of the Day)
CALLER: Is this Gordon’s Pizza?
GOOGLE: No sir, it’s Google Pizza.
CALLER: I must have dialed a wrong number. Sorry.
GOOGLE: No sir, Google bought Gordon’s Pizza last month.
CALLER: OK. I would like to order a pizza.
GOOGLE: Do you want your usual, sir?
CALLER: My usual? You know me?
GOOGLE: According to our caller ID data sheet, the last 12 times you called you ordered an extra-large pizza with three cheeses, sausage, pepperoni, mushrooms and meatballs on a thick crust.
CALLER: OK! That’s what I want …
GOOGLE: May I suggest that this time you order a pizza with ricotta, arugula, sun-dried tomatoes, and olives on a whole wheat gluten-free thin crust?
CALLER: What? I detest vegetables!
GOOGLE: Your cholesterol is not good, sir.
CALLER: How the hell do you know!
GOOGLE: Well, we cross-referenced your home phone number with your medical records. We have the result of your blood tests for the last 7 years.
CALLER: Okay, but I do not want your rotten vegetable pizza! I already take medication for my cholesterol.
GOOGLE: Excuse me sir, but you have not taken your medication regularly. According to our database, you only purchased a box of 30 cholesterol tablets once, at Drug RX Network, 4 months ago.
CALLER: I bought more from another drugstore.
GOOGLE: That doesn’t show on your credit card statement.
CALLER: I paid in cash…. I have other sources of cash.
GOOGLE: That doesn’t show on your last tax return unless you bought them using an undeclared income source, which is against the law. But you did not withdraw enough cash according to your bank statement.
CALLER: WHAT THE HELL!
GOOGLE: I’m sorry, sir, we use such information only with the sole intention of helping you.
CALLER: Enough already! I’m sick to death of Google, Facebook, Twitter, WhatsApp and all the others. I’m going to an island without internet, cable TV, where there is no cell phone service and no one to watch me or spy on me.
GOOGLE: I understand sir, but you need to renew your passport first. It expired 6 weeks ago.