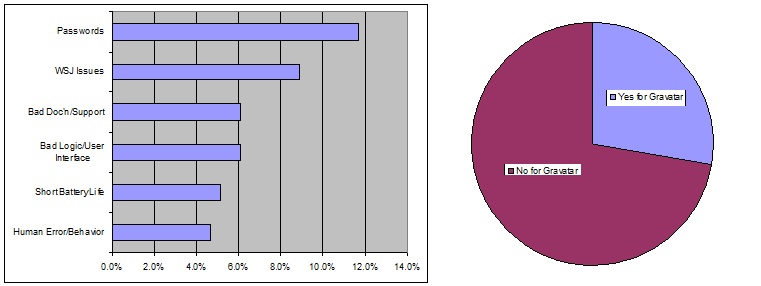
If something can go wrong, it will. And in the millions, nay billions, nay trillions (or more) of lines of code that comprise the Internet and its many websites (the total reached 1 billion in September 2014) that there are countless opportunities for errors or loopholes that let the bad guys (AKA hackers) wreak havoc. And that havoc can affect millions of innocent victims. The extent of the hacking during the past few years is enormous as can be seen from an interesting infograph.
In another recent episode that demonstrated the increasing ease of hacking, shady securities traders stole announcements from Business Wire, PR Newswire, and Marketwired after it was uploaded by the companies but before it was released to the public, and made millions by trading ahead of the public. (The former, harder method was to recruit company “insiders” to get advance tips.)
And there may be some recent disasters that were self-inflicted, e.g., the outages at the NYSE and United Airlines. Absent an identified villain, we would attribute those to faulty code that is so complex it is impossible to test thoroughly and to change as the environment changes.
Hacking has even become so widespread, and apparently so easy, that one of the leading anti-hacking software companies, the Italian company Hacking Team was recently hacked itself.
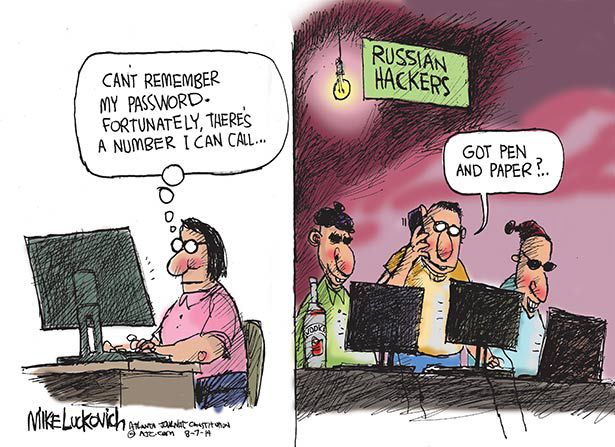
Even more scary is the almost certain hacking by unfriendly nations’ government-sponsored hackers (China, Russsia, etc.). Some of it is stealing commercial intellectual property, which can undermine the US’s economic strength (and directly or indirectly its military strength). Other of it can be military secrets, the loss of which can compromise the national security.
In the ultimate irony, The Wall Street Journal pointed out that while the giant tech firms like Apple, Facebook, and Google encrypt their data they don’t cooperate with the US government to searches that are legal under the Fourth Amendment of the Constitution.